
Creating a Private Network & Tunneling
Available Options
There are several options to create a private network and tunneling. I will be mentioning the most common ones, and we will implement the easiest.
- OpenVPN
- Wireguard
- TailScale
OpenVPN
OpenVPN is a system designed for establishing secure connections between different locations or devices over a virtual private network. It offers various methods for authentication, including pre-shared secret keys, certificates, or usernames/passwords. It can be used in both client and server applications, allowing the server to issue authentication certificates to clients in a multiclient-server setup. OpenVPN relies on the OpenSSL encryption library and the TLS protocol, incorporating numerous security and control features. It employs a proprietary security protocol that utilizes SSL/TLS for exchanging encryption keys. For more information, please visit OpenVPN.
Installing OpenVPN can be challenging due to several factors. Firstly, OpenVPN requires a certain level of technical expertise and familiarity with networking concepts. Configuring the server and client applications, setting up encryption keys, and establishing secure connections can be complex for individuals without a strong background in networking. Additionally, OpenVPN often requires manual configuration of various parameters, which can be time-consuming and error-prone. Troubleshooting connectivity issues and resolving compatibility problems with different operating systems or network environments can further contribute to the difficulty. Furthermore, the diverse range of available options and configurations in OpenVPN can be overwhelming for beginners, making it harder to navigate and customize the setup to meet specific requirements. Overall, while OpenVPN provides robust security and flexibility, its installation complexity can pose a significant barrier for users without sufficient technical knowledge or experience.
Wireguard
WireGuard is a free and open-source software application and communication protocol that implements virtual private network (VPN) techniques to create secure point-to-point connections in routed or bridged configurations. It is run as a module inside the Linux kernel and aims for better performance than the IPsec and OpenVPN tunneling protocols. For more information, please visit Wireguard.
Installing WireGuard can present certain difficulties for users, although it is generally considered easier than some other VPN protocols. One challenge is that WireGuard is relatively new compared to established VPN technologies like OpenVPN. As a result, it may not be as extensively documented or supported by various operating systems and platforms. This can lead to compatibility issues or limited availability of installation guides and troubleshooting resources. Additionally, configuring WireGuard often requires manual setup of network interfaces, IP addresses, and routing tables, which can be daunting for those who are less familiar with networking concepts. Furthermore, since WireGuard utilizes a different approach to VPN encryption, it may not have as wide a range of prebuilt packages or graphical user interfaces compared to more established VPN solutions. These factors can contribute to the perception of WireGuard installation as being more challenging, particularly for users who are not well-versed in networking or prefer a more streamlined installation process.
TailScale
TailScale is a mesh VPN that makes it easy to connect your devices, wherever they are. It works by installing a small daemon on each of your devices. The daemon connects to the TailScale service, which then routes traffic between your devices. For more information, please visit TailScale.
Installing Tailscale is generally considered easy due to several factors. First and foremost, Tailscale is designed with a strong emphasis on user-friendliness and simplicity. The installation process typically involves downloading and running a straightforward installer or package manager command, which automates much of the setup. Tailscale's intuitive graphical user interface further simplifies the configuration process, allowing users to easily authenticate and connect their devices with just a few clicks. The software also integrates seamlessly with popular operating systems, eliminating the need for complex network configurations or manual setup steps. Additionally, Tailscale's comprehensive documentation and helpful resources provide clear instructions and troubleshooting guidance, ensuring that users can quickly resolve any potential issues they may encounter. Overall, Tailscale's emphasis on user experience and streamlined installation process makes it accessible and hassle-free for users, even those without extensive technical expertise in networking.
Installing Tailscale on Server
Registering
Tailscale main mesh network is free for personal use, which allows up to 3 users and 100 devices. It supports basic identity provider integration, such as Google, GitHub, and Microsoft. In order to start, you need to register with Tailscale. You can register from offical page. Note that whatever provider you use, neither Tailscale nor the provider will have access to your traffic or data. They only use your identity to authenticate you.
Installing the Server Node and Configuration
First, we add Tailscale's package signing key and repository:
curl -fsSL https://pkgs.tailscale.com/stable/debian/bullseye.noarmor.gpg | sudo tee /usr/share/keyrings/tailscale-archive-keyring.gpg >/dev/null
curl -fsSL https://pkgs.tailscale.com/stable/debian/bullseye.tailscale-keyring.list | sudo tee /etc/apt/sources.list.d/tailscale.listsudo apt-get update
sudo apt-get install tailscaleecho 'net.ipv4.ip_forward = 1' | sudo tee -a /etc/sysctl.d/99-tailscale.conf
echo 'net.ipv6.conf.all.forwarding = 1' | sudo tee -a /etc/sysctl.d/99-tailscale.conf
sudo sysctl -p /etc/sysctl.d/99-tailscale.confetc/ufw/sysctl.conf file:
sudo nano /etc/ufw/sysctl.confnet/ipv4/ip_forward=1 and net/ipv6/conf/default/forwarding=1. Save and close the file. Next, we need to allow traffic forwarding in ufw:
sudo nano /etc/default/ufwDEFAULT_FORWARD_POLICY="DROP", and change the value from DROP to ACCEPT. Save and close the file. Now we can reload ufw:
sudo ufw disable && sudo ufw enablesudo tailscale up --advertise-exit-node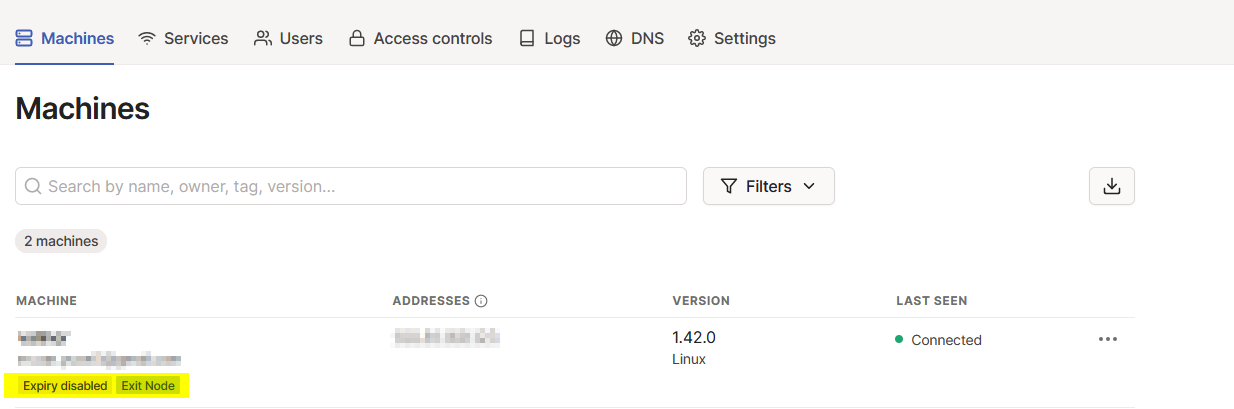
Now we don't want to keep authenticating in our server, so we click on the three dots at the right and select "Disable key expiry", so that we don't need to authenticate again. This is it, now our server is ready to be an exit node.
Installing on Android
We can install Tailscale on Android from Google Play. After installing, we need to authenticate our device with the same method we used for our server. After authenticating, we need to set our server as the exit node. We can do this by clicking on the three dots at the right and selecting "Set exit node". Now our Android device is ready to use our server as an exit node. This is it, now we can connect to our server from our Android device. You can check our IP address from here.
Installing on Windows
We can install Tailscale on Windows from official page. After installing, we need to authenticate our device with the same method we used for our server. After authenticating, we need to set our server as the exit node. We can do this by clicking on the three dots at the right and selecting "Set exit node". Now our Windows device is ready to use our server as an exit node. This is it, now we can connect to our server from our Windows device. You can check our IP address from here.